Innenminister Zimmermann traute seinen Ohren nicht. Da gab es wirklich „erwachsene Richter“, die sich die „Randbedenken“ einer radikalen Minderheit gegen die Volkszählung zu eigen machten. Und schlimmer: In einem Grundsatzurteil formulierten Verfassungsrichter Monate später, was sich auf lange Sicht als visionär erweisen sollte:
„Freie Entfaltung der Persönlichkeit setzt unter den modernen Bedingungen der Datenverarbeitung den Schutz des Einzelnen gegen unbegrenzte Erhebung, Speicherung, Verwendung und Weitergabe seiner persönlichen Daten voraus. (…) Das Grundrecht gewährleistet insoweit die Befugnis des Einzelnen, grundsätzlich selbst über die Preisgabe und Verwendung seiner persönlichen Daten zu bestimmen.“
Aus dem Volkszählungsurteil des Bundesverfassungsgerichts, Dezember 1983
Doch wer hätte in Jahr 1983 gedacht, dass wir einmal in einer Welt leben, in der die Menschen ihre Daten „unbegrenzt“ selbst zur Verfügung stellen? Was kein Problem wäre, wenn es sich eben nicht um „persönliche“ Daten handeln würde. Denn sobald sich Daten auf eine Person zurückführen lassen, beginnt sich das Interesse an Profilbildung zu regen. Die Schwierigkeit, Daten wirksam zu anonymisieren und das mangelnde Bewusstsein, warum man seine Identität schützen sollte, sind ein Grund dafür, warum man das Internet als kaputt bezeichnen könnte. Zeit, es zu reparieren und das uns überrollende Rad neu zu erfinden.
Digitale Selbstbestimmung steht und fällt mit dem zentralen Begriff der Identität
Wie prüfen wir eine Identität? Unser alltäglicher Identitätsnachweis funktioniert über einen möglichst einmaligen „Marker“: Name, Handynummer, Pass, eine Unterschrift, ein bekanntes Gesicht. Wie einmalig und überprüfbar diese Marker sind, misst sich an den Anforderungen. Am Flughafen ist man natürlich strenger als im Coffeeshop an der Ecke.
Zunehmend sind wir auch für Computer eindeutig erkennbar. Unser Handy scannt unseren Fingerabdruck, um sich zu entsperren. Bei Behörden oder im Krankenhaus, in alltäglichen Vertrags- und Kundenbeziehungen – überall ist es interessant, genau zu wissen, wer wer ist. Das schafft Vertrauen oder berechtigt zu Leistungen. Und wo wir dabei sind, verknüpfen wir unser digitales Ich zunehmend (und oft sorglos) mit allem Möglichen. Viele Menschen loggen sich z.B. auf allem möglichen Webseiten mit ihrem Facebook-Account ein. Andere nutzen eine Gesundheits-App.
Konfektionsgrößen, Bonität, tägliche Verkehrswege, Suchanfragen – all dies hilft den Algorithmen, uns personalisierte Angebote zu machen oder unser Verhalten vorherzusagen. Aus den vielen Datenpunkten, die wir im Stundentakt hinterlassen, könnten allwissende Computer ein extrem umfassendes Modell unserer Eigenschaften, Vorlieben und Gewohnheiten errechnen.
Könnten? Sie tun es längst. Zumindest, solange wir ihnen sagen, wer wir sind.
Der bisher einzige Weg, diesem System zu entkommen, war es, auf Verknüpfungen zu verzichten, sich z.B. von Social Media fernzuhalten, diskrete Browser zu nutzen und datensparsam zu leben. Mit zunehmender Vernetzung ist dieses Modell nicht mehr haltbar. Dingend gefragt sind daher Techniken, die es uns ermöglichen, unsere Identität punktuell und zuverlässig nachzuweisen, ohne dass daraus ein „gläserner Bürger“ modelliert werden kann. Und dazu gibt es vielversprechende Ansätze, die zur Zeit entwickelt und getestet werden. Man spricht – unter anderem – von Self-Sovereign Identities (SSI).
Die Rückeroberung des digitalen Ichs
„Identität steht im Mittelpunkt jeder Interaktion. Während das erforderliche Maß an Vertrauen zwischen den Identitäten von Interaktion zu Interaktion variieren kann, ist die Notwendigkeit, sie sicher und unter Wahrung der Privatsphäre auszutauschen, universell.“
In mühsamer Arbeit werden derzeit z.B. vom W3C und dem Sovrin-Netzwerk Standards entwickelt, die es ermöglichen sollen, anonyme und dennoch verlässliche Interaktionen im Digitalen herzustellen. Die Grundlage dafür soll ein System von digitalen Identitätsmarkern („DID“) bieten, die einmalig und ewig gültig sind und für jede einzelne Interaktion erstellt werden können. Mithilfe eines Schlüsselpaares und einer öffentlich zugänglichen Blockchain ist überprüfbar, dass die betreffende DID authentisch ist.
Inhaltlich ist es dabei egal, ob der Ersteller (Issuer) das Meldeamt ist oder meine Oma. Auch der Anlass kann noch so geringfügig sein – es sind genügend DIDs für alle da. DIDs können zum Beispiel sagen „Diese Person …
- … ist in unserem Yogastudio Kunde*in Nr. 123 mit einem Bonusguthaben.“
- … ist bei uns Mitarbeiter*in und darf das Haus betreten.“
- … hat einen Presseausweis.“
- … wurde gegen Masern geimpft.“
- … ist im Besitz eines gültigen Führerscheins und über 21 Jahre alt.“
- … hat die Buchsendung XY bezahlt und darf das Paket in Empfang nehmen.“
Verknüpft ergeben die Informationen ein zunehmend komplexes Bild der Person – einzeln enthalten sie nur die relevante Information. Denn eigentlich interessiert ja nur, dass die DID für die jeweils infrage stehende Eigenschaft zuverlässig bürgt. Und nicht, ob das Gegenüber sich außerdem für Katzen oder Hunde interessiert. Gegenüber z.B. einer Bank können wir dann aus unserem Portfolio (Wallet) genau das Set an Informationen freigeben, die diese wirklich benötigt. Und diese kann die Informationen absolut zuverlässig verifizieren.
Wir müssen verstehen, dass Anonymität nichts für Verbrecher ist, sondern der entscheidende Baustein für unsere freiheitliche Zukunft
Der Begriff „anonym“ weckt Ängste – und manche Politiker bemühen sich nach Kräften, diese zu schüren. Inzwischen wird aber deutlich, dass wir unsere digitale Souveränität längst in dubiose Hände abgegeben haben. „Abuse of power comes as no surprise“ – Die Staatslenker dieser Welt wie auch die übermächtigen Internet-Monopolisten verfolgen jeweils eigene Interessen. Eine Klarnamenpflicht bei Facebook, eine staatliche Backdoor für Nachrichten-Apps, die Payback-Karten oder der staatliche Blick in den Amazon-Account – wir lernen zunehmend, dass es nicht die Ausnahme sein darf, im Cyberspace anonym zu sein, sondern es muss die Regel werden.
Wie werden also die Anforderungen an fortschrittliche DID-Infrastruktur formuliert?
- Sie muss interoperabel sein, also allen offen stehen.
- Sie muss dezentral sein, also nicht einer einzelnen Autorität unterliegen.
- Sie muss verifizierbar sein, also unbestechlich und stets für alle überprüfbar.
- Sie muss die Anonymität der Beteiligten wahren, nur ich kontrolliere mein Wallet.
Der Blockchain Bundesverband schreibt dazu in seinem Positionspapier:
„Im Modell der Self-Sovereign Identity können Personen und Institutionen ihre Identifikatoren dezentral erstellen und verwalten, ohne auf einen Drittanbieter angewiesen zu sein. Im Gegensatz zu bestehenden Lösungen, die aus der Perspektive der Organisation strukturiert sind, die einen Identifikator vergibt, sind selbstsouveräne Identitäten strukturell so konzipiert, dass sie aus der Perspektive der Person oder Institution funktionieren, die das Subjekt eines bestimmten Identifikators ist.“
Wie funktioniert das Ganze nun – und warum erst jetzt?
Schon oft haben sich schnelle technische Lösungen gegenüber nachhaltigen durchgesetzt. Über das Thema Identität im Internet hat man früh nachgedacht, ist aber erst aus Schaden klug geworden. Auch die Blockchain, auf der SSI basiert, hat sich als Technik überraschend langsam herumgesprochen (Bitcoin gibt es seit 10 Jahren), ist heute aber Grundlage vieler digitaler Praktiken wie Smart Contracts oder Auditing. Self-Sovereign Identities in Gänze zu erklären, sprengt hier den Rahmen und andere können das besser (hier kurz und hier länger).
Hier daher nur das Wichtigste in Kürze:
Im Gegensatz zu „normal“ vergebenen Identitätsmarkern (Pass, Login etc.) oder von Dritten verwalteten IDs („federated ID“) gibt es bei der Self-Sovereign Identity keinen von irgendjemand kontrollierten Server. Alle IDs werden auf eine Blockchain geschrieben, die zwischen etlichen Servern geteilt wird (Distributed Ledger) und damit gegen einzelne Manipulationen geschützt ist. Sie dient der Verifizierung der in beliebiger Menge erstellten DIDs, die mit Hilfe von Verschlüsselung anonym sind. Niemand weiß, wem ein Schnipsel einer Blockchain zugeordnet ist, aber jeder kann prüfen, dass er da ist. Es gibt damit keine Stelle mehr, die sämtliche Informationen über eine Person einander zuordnen kann. Und alle Akteure sind gleichrangige Mitglieder (Peers) in einem für alle zugänglichen Netzwerk.

Das Prinzip der Self-Sovereign Identity ist es, dass beide Partner der Interaktion gleichwertige Partner auf einer fälschungssicheren Basis sind.
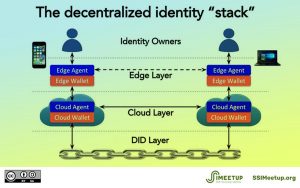
Das Prinzip der DID bildet die Grundlage für eine Infrastruktur von anonymen aber verifizierbaren Identitäts-Schnipseln.
DIDs werden in digitalen Brieftaschen (Wallets) gesammelt und bei Bedarf wie Passwörter übertragen – nur das man sie sich nicht merken muss. Auf dieser technischen Grundlage können Apps, Behörden, Messengerdienste, Soziale Netzwerke und wer-auch-immer ihre Sicherheitsarchitekturen aufbauen, ohne Manipulationen befürchten zu müssen. So können höher gelagerte Verträge adressiert werden, die sich auf einer anderen Ebene abspielen, nicht mehr in der Blockchain. Man erhält damit damit genau das Maß an Anonymität oder Offenlegung, dem beide Akteure zustimmen. Monopolisierende Standards von staatlichen oder privaten Stellen werden überflüssig.
Pro – und Contra?
Die Auswirkungen einer solchen Infrastruktur sind unübersehbar. Was der Bitcoin für das Finanzsystem ist – eine Währung, deren Regeln nicht kontrolliert werden, sondern im Code festgelegt sind – können Self-Sovereign Identities bald im restlichen digitalen Kosmos werden. Dieser Werkzeugkasten rückt die verloren gegangene und von der Verfassung zugesicherte „Informationelle Selbstbestimmung“ zurück in den Bereich des machbaren. Wir werden in Zukunft häufiger selbst entscheiden können, wem wir vertrauen. Welche Politikerin, welcher Politiker wollte das nicht begrüßen und unterstützen?
Doch es gehört nicht viel Fantasie zu der Vorstellung, dass Self-Sovereign Identities nicht nur Freunde haben werden. Diverse Akteure profitieren ja davon, dass wir in unserer technisierten Kommunikation Spuren hinterlassen, aus denen sie Profile bilden. Marketing-Strategen gehören dazu ebenso wie Trollfabriken, die Politische- oder Religions-Polizei in totalitären Staaten ebenso wie die hiesige Kriminalpolizei, die sich nun andere Methoden einfallen lassen muss. Wie soll China auf dieser Grundlage seine volkserzieherische Überwachungspolitik durchhalten? Vielleicht wird es sogar Kampagnen gegen SSI geben oder werden Zweifel gestreut, dass das System funktioniert.
Eine Kampagne gegen SSI wäre etwa so sinnvoll, wie eine Kampagne gegen den Bitcoin oder das Darknet. Gegen die Entwicklung an sich sind selbst die stärksten Akteure machtlos. Auch eine Einflussnahme, etwa von Geheimdiensten, ist angesichts offener Quellcodes wenig erfolgversprechend. Und wohin sich die Bürger*innen, Unternehmer*innen oder Verbraucher*innen am Ende wenden werden ist ihnen selbst überlassen.
//
Cartoon mit freundlicher Genehmigung von Ian Baker
Weiterführende Links
… zum Thema Anonymität im Internet:
… zu Self-Sovereign Identities:
Video zu DID (englisch, 10 Min.)
Ausführlicher Artikel auf trendreport.de
Ausführlicher Artikel auf bitcoinblocks.net (auf englisch)
Keynote eines Entwicklers (englisch, 1 h)
Neue Vokabeln und Buzzwords zum Nachschlagen:
Anonymous Attribute Systems
Blockchain
Curated Identities
DDI (Decentralised Digital Identity)
DID = Decentralised Identifier (SSI-Stadard, wird entwickelt vom W3C)
DID Auth (SSI-Stadard zur Authetifizierung, wird entwickelt von DIF / IETF)
DKMS = interoperable key management (SSI-Stadard, wird entwickelt von OASIS)
Digital Wallet (Zugangs-Sammlung)
Distributed Ledgers
Etherium (Blockchain-Anwendung)
Federated identity
IAM (Identity and Access Management, deutsch: IdM bzw. Identitätsmanagement)
KNY (Know your customer)
PKI (Public Key Infrastructure)
Smart Contracts (technisch ausführbare Regelungen)
SSO (Single Sign-on)
SSI (Self-Sovereign Identities)
Token (Wertmarke)
Veryfiable Credentials (SSI-Stadard für verifizierbare Zugänge, wird entwickelt vom W3C)